Work from home has skyrocketed in 2020, and so has data loss. According to an article in CIO Dive, the biggest security challenge of remote work is insider threats and identifying the location of malicious activity. Understanding whether documents are being improperly accessed, how users are using them and whether irregular login patterns are occurring is important for high-value regulated data. Understanding user activity is essential not only to keep mission critical content apps running smoothly but to help organizations protect against data loss and prepare for compliance audits. And when the data includes business-critical content residing in secured repositories, you should know who downloads it.
Key ECM User Metrics
At a minimum you need to be able to answer the following questions to measure and understand how you content is being used, establish a baseline and identify any suspicious activity:
- Do you know your best or power enterprise content management (ECM) app users?
- Does any content access appear suspicious from unknown geo locations?
- How has remote work changed ECM app adoption and usage?
- Are users exporting or downloading large numbers of files?
- Can you provide audit reports documenting access to sensitive information?
The answers to these questions will help you pinpoint any service level issues, adjust access permissions, and assess ongoing training needs. For example, perhaps users are avoiding an app because additional training is necessary, or they just can’t find what they need in a timely manner. Or, if you have multiple sites, users may be leveraging some repositories or sites more than others, making them redundant.
Unfortunately getting visibility into user behavior and content access metrics, especially if you’re using multiple content platforms, often requires a lot of customized reporting. This can be cumbersome and time consuming to build out, not to mention competes with other IT priorities.
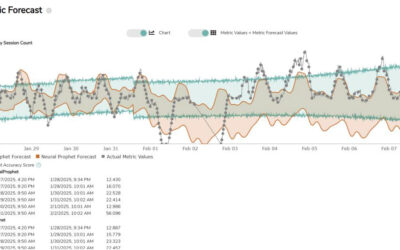
Do More with Less Using Reveille
With Reveille customers gain deep, contextual intelligence about access to and user behavior surrounding high-value, business-critical content. With out-of-the-box reports and monitoring for a wide range of enterprise ECM applications, Reveille’s provides immediate insight into user activity in context, content security and compliance auditing. Reveille helps detect, speed the investigation of and reduce the impact of a data breach by identifying suspicious access to content within your ECM / content services platforms (CSP).
Get detailed, actionable insight on:
- When users access applications and how they are using them
- Content access patterns indicative of a security anomaly
- Content use / misuse indicative of insider threats
- Irregular document access by privileged insiders
- Suspicious login attempts from both inside and outside of the corporate network
- High volume movement of data to endpoint devices
- Irregular download/upload volumes
- Set maximum export thresholds with automated notifications if surpassed
Reveille can automatically shut down suspicious user access based on conditions set by the business to dramatically reduce the impact of a content breach from malicious insiders or hackers posing as your trusted insiders.
With Reveille user analytics you can easily establish a baseline of content access, identify app training needs (how to search, what to index), improve content assets location (balance performance with storage placement), be audit ready with compliance evidence, mitigate suspicious access, reduce data exfiltration, identify hot content for review, and more.
Sound interesting? Give us 2 minutes.
Watch this short demo to see how Reveille provides insight into the security of your content, as well as ECM performance without the heavy lifting.